NIS2 Compliance in 2026: What EU CISOs and Counsel Must Do Next
In Brussels this week, regulators reiterated an uncomfortable truth: NIS2 compliance is no longer a future project—it’s a present-tense obligation for essential and important entities across the EU. Between stepped-up enforcement, evolving EU regulations, and a rash of high-impact cyber incidents, the margin for error has narrowed. A CISO I interviewed in Frankfurt put it bluntly: “We can’t spreadsheet our way through NIS2 anymore—governance and verifiable controls are the new audit baseline.”

From supply-chain flaws to social engineering at scale, the threat landscape hasn’t eased. Law enforcement disruptions of malicious infrastructure highlight how pervasive botnets have become, while shifts in mainstream messaging platforms’ encryption features remind compliance teams not to rely on consumer apps for sensitive operations. Add in misunderstood proofs-of-concept for network devices fueling chaos and you get the same bottom line: cybersecurity compliance now demands a proactive, evidence-based program that spans risk management, incident reporting, and data protection—backed by secure workflows for personal data, anonymization, and document handling.
Who is in scope for NIS2 compliance?
NIS2 (EU Directive 2022/2555) expands the number of covered sectors and tightens minimum-security requirements. If you operate in the EU and fall into any of the following categories, you are likely in scope as an essential or important entity:
- Energy, transport, banking, financial market infrastructures
- Health, drinking water, waste water, pharmaceuticals, medical devices
- Digital infrastructure (IXPs, DNS, TLDs), data centers, cloud, content delivery
- Public administration (as defined nationally)
- Space, manufacturing of critical products, postal and courier services
- Waste management, food production and distribution
- Providers of managed services and certain ICT services
Member States determine the precise designation, but the presumption under NIS2 is that medium and large organizations in covered sectors are in scope unless exempted by specific criteria.
NIS2 compliance milestones, reporting, and penalties
- Incident reporting: Early warning to the CSIRT/competent authority within 24 hours of becoming aware; an initial assessment within 72 hours; and a final report within one month detailing root cause and mitigation.
- Management accountability: Boards must oversee cybersecurity risk management; failure can trigger corrective orders and temporary suspensions of responsible personnel (for essential entities).
- Risk management measures: Policies, incident handling, business continuity, supply-chain security, vulnerability handling, secure development, encryption, MFA, logging, and security audits.
- Penalties for non-compliance:
- Essential entities: up to at least €10 million or 2% of global annual turnover (whichever is higher).
- Important entities: up to at least €7 million or 1.4% of global annual turnover (whichever is higher).
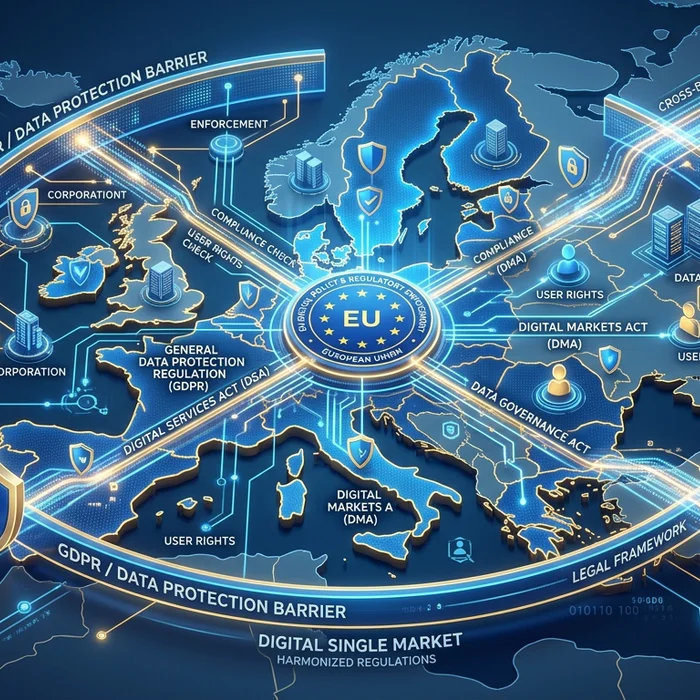
GDPR vs NIS2: obligations compared
Legal, risk, and security teams often ask how GDPR and NIS2 intersect. Use this side-by-side to calibrate responsibilities:

| Topic | GDPR | NIS2 |
|---|---|---|
| Primary focus | Data protection and privacy of personal data | Cybersecurity risk management and resilience of essential/important entities |
| Scope | Controllers/processors handling personal data | Sector- and size-based (essential/important) entities |
| Incident reporting timeline | Notify supervisory authority within 72 hours of personal data breach (if risk to rights/freedoms) | Early warning within 24 hours; initial reporting by 72 hours; final report within one month |
| Governance | DPO where required; DPIAs for high-risk processing | Board-level accountability; mandatory risk management measures |
| Supply-chain security | Processor due diligence and contracts | Explicit supplier and service-provider risk management obligations |
| Sanctions | Up to €20m or 4% of global turnover (whichever higher) for certain infringements | Up to at least €10m/2% (essential) or €7m/1.4% (important) |
| Technical measures | Appropriate security (Art. 32), pseudonymization/anonymization recommended | Baseline measures: incident handling, continuity, testing, logging, secure design, encryption, MFA |
NIS2 compliance checklist (practical, audit-ready)
- Governance: Assign board oversight; define risk appetite; update policies with NIS2 references.
- Asset inventory: Maintain live inventories of systems, data flows, and third parties.
- Risk management: Run threat-led risk assessments; document treatment plans.
- Logging and monitoring: Centralize logs; set thresholds; rehearse alert triage.
- Vulnerability management: Continuous scanning, patch SLAs, exposure reduction.
- Secure development: Threat modeling, code review, SBOMs for critical software.
- Access security: MFA, least privilege, privileged access management, segmentation.
- Backup and continuity: Immutable backups, restoration drills, RTO/RPO mapped to business impact.
- Incident response: 24h/72h/1-month playbooks; regulator contact points; dry runs.
- Supply-chain controls: Security clauses, evidence-based assurance, right-to-audit, fourth-party mapping.
- Training: Role-based exercises for SOC, legal, PR; phishing and mobile-first awareness.
- Data protection: DPIAs where needed; privacy-by-design; strong anonymization for analytics/AI.
- Evidence: Keep proof of controls, tests, and board briefings for security audits.
Why 2026 feels different: three live pressures
- Regulatory heat: Member States are ramping up supervision; cross-border coordination reduces “forum shopping.”
- Operational tail risk: Fake exploit code and misunderstood PoCs are driving misconfigurations in complex SD-WAN and edge stacks.
- Mobile and messaging risk: Smartphone-driven phishing and shifting encryption defaults on consumer apps make data exfiltration easier to miss.
For banks, hospitals, and law firms, the pattern is clear: privacy breaches now trigger simultaneous GDPR and NIS2 scrutiny. Containing exposure means locking down personal data, hardening document workflows, and proving you can report within 24–72 hours with facts, not guesses.
Data handling under NIS2 and GDPR: anonymization and secure document uploads
Two recurring audit findings I see: (1) sensitive attachments floating through chat and email, and (2) analysts feeding unredacted case files into AI tools. Both create avoidable compliance risk.
- Before sharing or processing case files, strip identifiers using an AI anonymizer that can reliably redact personal data, health data, and payment details.
- Centralize secure document uploads—avoid ad hoc attachments across consumer messaging apps.
Professionals avoid risk by using Cyrolo’s anonymizer at www.cyrolo.eu. And if your team needs to review discovery bundles or incident logs, try secure document uploads at www.cyrolo.eu—no sensitive data leaks, and a clear trail for security audits.
Compliance reminder: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.
Real-world snapshots: from boardroom to SOC
- Banking: A regional lender’s red team found privileged credentials in ticket attachments. Solution: mandatory secure document uploads, automated redaction before tickets leave the source system, and tighter PAM.
- Healthcare: A hospital’s clinical AI pilot ingested unmasked radiology notes. Solution: enforce pre-ingestion anonymization and keep AI workflows in a ring-fenced environment with evidence of DPIAs.
- Law firm: Associates shared draft exhibits via consumer chat during travel. Solution: ban shadow comms for client work, enforce enterprise SSO + MFA, and route all evidence through a secure upload and review portal.
Implementation guide: align controls to the directive
- Map scope and designate accountable owners: Identify essential/important entities in your group; assign an exec sponsor and a program manager.
- Baseline against NIS2 measures: Use the checklist above; gap assess current policies and controls.
- Prioritize reporting readiness: Build the 24h early-warning workflow with legal and comms; template the 72h and one-month reports.
- Integrate data minimization: Replace raw sharing with robust anonymization; prove it via test datasets and sampling.
- Harden supply-chain evidence: Demand control attestations, test restores for backup providers, and SBOM visibility for critical software.
- Measure, test, improve: Track KPIs (patch latency, phishing resilience, MTTD/MTTR) and hold quarterly board briefings—documenting decisions.
How Cyrolo supports GDPR and NIS2 teams
Cyrolo helps close two persistent audit gaps: identifiable data in working files, and uncontrolled file sharing.
- AI anonymizer that detects and removes personal data, including health and financial identifiers—supporting GDPR data protection by design.
- Secure document uploads with controlled access and audit trails—aligning to NIS2’s evidence-driven approach to incident handling and supplier oversight.
Try the anonymizer and compliant document upload workflow at www.cyrolo.eu. Your legal, risk, and security teams get the same thing regulators want: verifiable, repeatable controls that reduce breach impact.
FAQs: NIS2 compliance, GDPR, and practical steps
What is NIS2 compliance in simple terms?
It means implementing and evidencing risk-based cybersecurity controls, reporting serious incidents on a 24h/72h/1-month schedule, and maintaining accountable governance for essential and important entities in the EU.
How does NIS2 interact with GDPR?
NIS2 targets operational resilience and incident reporting; GDPR targets personal data protection. A single incident can trigger both regimes if systems and personal data are affected, so integrate legal, security, and privacy playbooks.
What are the NIS2 incident reporting deadlines?
Early warning within 24 hours of awareness, an initial report within 72 hours, and a final report within one month, including root cause and mitigation status.
Who falls under NIS2?
Medium and large organizations across specified sectors (energy, health, digital infrastructure, finance, manufacturing of critical products, public administration, and others). National rules finalize the designations.
How do I anonymize documents safely for AI or vendor sharing?
Use a proven AI anonymizer and a secure upload workflow so personal data is masked before sharing. Do not paste sensitive data into public tools. Consider www.cyrolo.eu for anonymization and secure document uploads.
Important: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.
The bottom line: make NIS2 compliance your operational habit
NIS2 compliance isn’t a once-a-year policy refresh; it’s a daily practice across governance, technology, and supplier oversight. Build muscle memory around 24/72/1-month reporting, document your decisions, and minimize exposure by anonymizing personal data and centralizing secure document uploads. If you need a fast, reliable way to operationalize those workflows, test Cyrolo’s anonymizer and upload tools at www.cyrolo.eu—and turn regulatory pressure into sustainable resilience.