NIS2 Compliance Checklist 2026: Practical Steps, GDPR vs NIS2, and How to Secure AI Document Workflows
In today’s Brussels briefing, regulators emphasized that 2026 is the year when NIS2 moves from policy to practice. If you’re searching for a clear NIS2 compliance checklist you can actually use, this field report distills what boards, CISOs, DPOs, and counsel need to do now—tying obligations to day-to-day operations, AI usage, and secure document handling. As I’ve heard repeatedly from European supervisors this quarter, “demonstrable implementation” will determine whether you pass a security audit—or face sanctions.

- Primary takeaway: NIS2 raises the bar on governance, incident reporting (24h early warning / 72h notification), and supply‑chain controls.
- GDPR still governs personal data; NIS2 governs network and information systems. You need both.
- AI and LLM adoption is now a board-exposure issue. Anonymize inputs and secure document uploads to prevent privacy breaches.
- Fines: GDPR up to €20m or 4% global turnover; NIS2 commonly up to €10m or 2% (Member State variations apply).
- Immediate wins: multi-factor authentication, vulnerability management, logging, tested incident playbooks, and safe AI pipelines.
Why NIS2 matters in 2026: enforcement reality
I’ve sat in on closed-door roundtables where EU regulators stressed three themes. First, boards are accountable: leadership must oversee cybersecurity risk, sign off on policies, and complete training. Second, incident reporting has teeth: early warning within 24 hours, a more detailed notification within 72 hours, and a final report within a month. Third, supply-chain assurance is no longer “nice to have”—expect auditors to probe how you vet vendors, SaaS tools, and AI services.
On the ground, CISOs tell me they’re still securing AI with yesterday’s tools. Meanwhile, phishing-led intrusions using off-the-shelf RATs keep succeeding, and malware now piggybacks on consumer messengers to reach corporate devices. NIS2 is designed for exactly this world: rapid detection, disciplined response, and traceable controls.
Your NIS2 compliance checklist (do this in the next 90 days)
This NIS2 compliance checklist is built for essential and important entities across finance, health, energy, transport, digital infrastructure, and managed services—plus professional services that support them (law firms, consultancies, MSPs).
Governance and risk
- Board oversight: Formally assign cybersecurity responsibility to the board; schedule quarterly risk reviews and require completion of role-based security training.
- Policies and risk assessment: Approve a NIS2-aligned risk management framework covering identity, access, patching, logging, backup, and business continuity.
- Supplier assurance: Tier vendors by risk; require security attestations and breach-notification SLAs; assess AI/LLM tools like any other high-risk SaaS.
Core technical controls
- Strong authentication: Enforce MFA for admins and all remote access; phase out SMS codes for higher assurance methods where feasible.
- Vulnerability and patch management: Maintain a 30/7/1 patch policy (30 days standard, 7 days high, 1 day critical with compensating controls where patching is impossible).
- Secure configuration and hardening: Baseline CIS/ENISA profiles; disable legacy protocols; rotate keys and secrets.
- Logging and monitoring: Centralize logs, retain forensically useful data, and create high-fidelity alerts for privilege misuse and data exfiltration.
- Encryption and backups: Encrypt data in transit/at rest; maintain offline, immutable backups; test recovery quarterly.
Incident response and reporting
- Playbooks: Maintain tested runbooks for ransomware, business email compromise, supplier compromise, and AI-model misuse (e.g., prompt injection data leaks).
- Reporting clock: Prepare “24/72/30” templates—24h early warning, 72h significant incident report, 30-day final report; map your national CSIRT contacts.
- Drills: Run cross-functional tabletop exercises every six months including legal, PR, data protection, and sector regulator liaisons.
Data protection and AI workflows
- Data minimization: Strip personal data before sharing logs, tickets, or AI prompts whenever possible.
- AI safety guardrails: Route staff to a secure anonymization workflow before any LLM use; block raw uploads of client files to public tools.
- Secure document handling: Use a vetted platform for document uploads that keeps files private, logged, and access-controlled.
Mandatory best practice reminder: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.

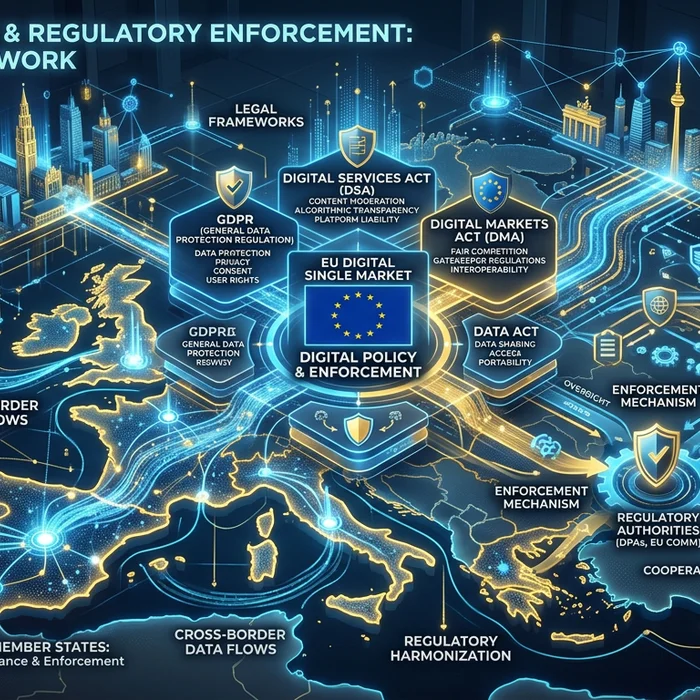
GDPR vs NIS2: where they align—and where they don’t
Legal teams often ask me whether GDPR “covers it all.” It doesn’t. GDPR protects personal data; NIS2 protects the availability, authenticity, integrity, and confidentiality of network and information systems. The result: two overlapping but distinct compliance lanes you must drive in at the same time.
| Topic | GDPR | NIS2 |
|---|---|---|
| Scope | Processing of personal data | Security of network and information systems for essential/important entities |
| Primary objective | Data protection and privacy rights | Cyber resilience and continuity of critical/important services |
| Security baseline | “Appropriate” technical/organizational measures; DPIAs | Risk management measures: MFA, patching, logging, supply-chain controls, BC/DR |
| Incident reporting | 72h to Data Protection Authority for personal data breaches | 24h early warning; 72h notification; final report within 1 month to CSIRT/competent authority |
| Penalties | Up to €20m or 4% global turnover | Commonly up to €10m or 2% global turnover (varies by Member State); management liability and audits |
| Who’s in scope | Controllers/processors of personal data | Essential and important entities in specified sectors and size thresholds |
AI, LLMs, and secure document uploads: NIS2 and GDPR expectations
AI is everywhere in EU enterprises, but I still see teams pasting raw client files into public LLMs without anonymization—an obvious GDPR and NIS2 failure. Supervisors increasingly ask to see your AI usage policy and the actual controls that enforce it: redaction before prompt, access controls, logging, and data residency. Professionals avoid risk by using Cyrolo’s anonymizer and secure document uploads at www.cyrolo.eu—no sensitive data leaks, auditable by design.
Two practical guardrails I recommend to every CISO I interview:
- Default-disable public LLM uploads from corporate networks; provide a sanctioned alternative with automated anonymization.
- Embed privacy-by-design into prompt templates: scrub names, emails, IDs, free-text PII before any AI analysis.
Reminder: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.

Sector snapshots: what “good” looks like in practice
Banks and fintechs
- 24/7 SOC with threat intel on banking malware and payment fraud; strict segregation of SWIFT/SEPA environments.
- Third-party risk management for core SaaS, PSPs, and AI coding assistants; contractual breach notice within 24h.
- Automated log correlation of payment anomalies and identity events; quarterly recovery tests for critical ledgers.
Hospitals and healthcare
- Network segmentation for clinical devices; rapid patching for imaging and lab systems; allowlists for vendor maintenance.
- Ransomware playbook aligned with patient safety; offline backups validated against tampering.
- Strict controls on clinical note uploads to AI tools—use anonymization before any triage or summarization.
Law firms and professional services
- Client confidentiality controls baked into DMS and eDiscovery tooling; tamper-proof logging of access to matter files.
- Prompt-redaction pipeline to remove personal data from memos before LLM drafting or review.
- SaaS whitelisting and a secure channel for document uploads during urgent filings.
What Brussels is signalling next
IMCO’s latest debate on competitiveness and defence R&I underscored a trend I’m tracking across committees: more funding and stricter expectations for cybersecurity across the supply chain. Expect procurement rules to reference NIS2-grade controls, and for security audits to expand into software lifecycle assurance. Translation: if you sell into regulated sectors, you’ll be asked to prove your controls—fast.
EU vs US: different roads, same destination
EU entities face horizontal obligations under GDPR and NIS2, enforced by national regulators and CSIRTs. The US is converging via sectoral rules (e.g., financial services), SEC incident disclosure expectations, and forthcoming critical infrastructure reporting regimes. Practically, multinationals are standardizing on the EU bar—MFA everywhere, rapid incident reporting, meaningful supplier assurance, and provable AI data protections.
Compliance checklist: proof points auditors expect to see
- Board minutes showing cybersecurity oversight and annual training completion.
- Risk register with timelines and owners; evidence of quarterly patch KPIs.
- MFA coverage reports for admins and remote users; legacy protocol deprecation plan.
- SIEM dashboards, retention settings, and incident ticket links; test alerts.
- Supplier tiering matrix; contracts with 24/72h incident obligations; recent audit reports.
- Incident drills with attendance records and improvement actions.
- AI usage policy; anonymization workflow; logs proving safe document uploads.
- Backup immutability evidence; quarterly restore tests.
- Staff awareness outcomes (phishing simulations, secure coding scores).
FAQ: NIS2, GDPR, and secure AI in 2026
What is NIS2 and who must comply?
NIS2 is the EU’s directive raising cybersecurity requirements for essential and important entities across sectors like energy, finance, health, transport, digital infrastructure, and managed services. Many professional services supporting these sectors are in scope, too. If you’re medium or large in a listed sector, assume you’re covered.
What are the NIS2 incident reporting timelines?
Submit an early warning within 24 hours of becoming aware of a significant incident, a more detailed notification within 72 hours, and a final report within one month. Align this with GDPR’s 72-hour breach rule when personal data is involved.
How does NIS2 interact with GDPR?
GDPR governs personal data processing and breach reporting to DPAs. NIS2 governs the resilience of your networks and systems, reported to your CSIRT/competent authority. Many incidents trigger both. Treat them as parallel tracks with shared evidence.
How can we safely use AI and LLMs under NIS2/GDPR?
Enforce data minimization and anonymization before prompts, restrict AI tool access, log usage, and keep data within approved jurisdictions. When in doubt, route staff to www.cyrolo.eu for safe anonymization and secure document uploads.
What proof will auditors ask for in 2026?
Board accountability, risk registers with KPIs, MFA coverage, vulnerability SLAs, logging and retention, tested IR playbooks, supplier due diligence, AI usage controls, and evidence you can meet the 24/72/30 reporting cadence.
Conclusion: turn your NIS2 compliance checklist into action
NIS2 is no longer theoretical. Use this NIS2 compliance checklist to harden controls, prove board oversight, and bring AI usage into a compliant, low-leak state. For high-velocity teams, the fastest win is to operationalize safe data handling: anonymize first and confine sensitive files to a secure pipeline. Try Cyrolo’s anonymizer and secure document upload at www.cyrolo.eu today—and sleep better before your next audit.