AI anonymizer for GDPR compliance: 2026 survival guide for NIS2, AI risk, and secure document uploads
As EU regulators turn up the heat, the fastest path to lower risk is deploying an AI anonymizer for GDPR compliance that your legal and security teams actually trust. In today’s Brussels briefing, officials reiterated that wearable devices, AI-driven malware, and supply-chain vulnerabilities are converging into a single regulatory reality: if you process personal data, you must prove robust data protection, secure document uploads, and continuous cybersecurity compliance under GDPR and NIS2.

Compliance note: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.
Why 2026 raised the stakes for privacy and security
I spent this week speaking with CISOs and DPOs from banks, hospitals, and fintechs after three eye-opening developments:
- Wearables and always-on cameras captured highly sensitive footage in private spaces — a reminder that bystanders’ personal data can be processed unlawfully, even when your company isn’t the device owner.
- A nation-state group industrialized AI-driven malware generation, accelerating phishing, payload customization, and evasion — a direct risk to regulated entities facing NIS2 security audits.
- Law enforcement dismantled a major phishing service as vendors raced to patch dozens of firewall vulnerabilities — underscoring the urgency of vulnerability management, segmentation, and incident reporting.
The takeaway from Brussels: Regulators expect mature controls that prevent privacy breaches before they happen, not post-incident apologies. That means minimizing personal data exposure at source (strong anonymization), ensuring secure document uploads, and proving you can detect, respond, and report security incidents under tight NIS2 timelines.
What GDPR and NIS2 demand — and where AI tools go wrong
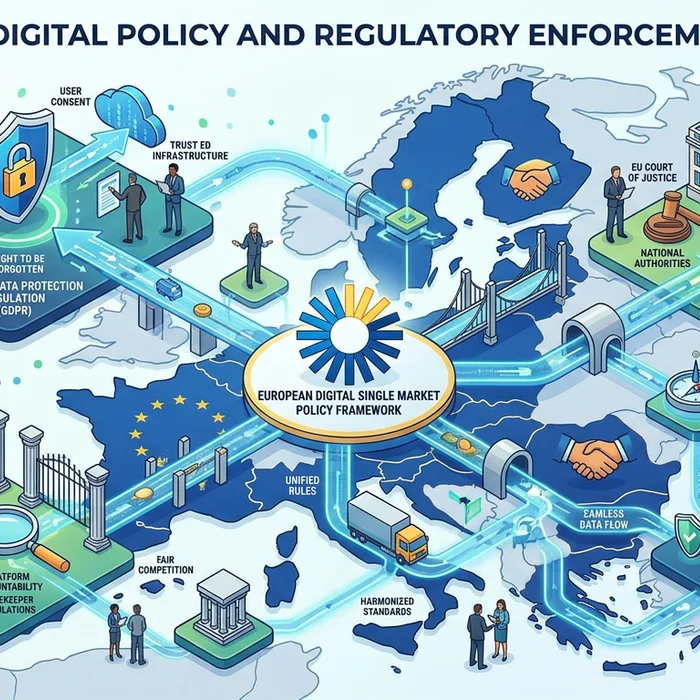
GDPR mandates data minimization and privacy by design. NIS2 raises the bar on cybersecurity governance, vulnerability management, and incident reporting. Both regimes now converge on a hard truth: ad hoc use of generative AI or unmanaged file sharing can become a documented compliance failure.
- Hidden data in files: PDFs, DOCs, and images often contain personal data and metadata. Without anonymization, uploads to AI tools may risk unauthorized processing and cross-border transfers.
- Shadow AI: Staff paste client details into online models. If logs or training traces persist, you’ve created evidence of unlawful disclosure.
- Wearable spillover: Teams ingest user-generated content from field devices; unredacted frames can expose sensitive categories of data.
Solution-focused teams standardize on a vetted anonymizer and a single secure intake for document uploads across legal, compliance, and security workflows.
GDPR vs NIS2: core obligations compared
| Topic | GDPR (Data Protection) | NIS2 (Cybersecurity) | What Teams Must Prove |
|---|---|---|---|
| Scope | All personal data processing by controllers/processors | Essential/important entities in key sectors and supply chains | Map data flows and critical systems; assign accountability |
| Data Minimization | Collect only what’s necessary; use anonymization/pseudonymization | N/A explicitly, but reduces attack surface and breach impact | Demonstrate robust, auditable anonymization for risky workflows |
| Security Measures | “Appropriate” technical and organizational controls | Risk management, patching, logging, crypto, supplier oversight | Document policies, tooling, and continuous control effectiveness |
| Incident Reporting | Notify data protection authorities and subjects if high risk | Mandatory reporting to CSIRTs/authorities on strict timelines | Playbooks, escalation paths, and evidence of timely reporting |
| Penalties | Up to €20M or 4% of global turnover (whichever is higher) | Up to ~€10M or 2% of global turnover (Member State variants) | Board-level oversight and budget to close compliance gaps |
| AI Usage | Lawful basis, DPIAs, high-risk processing controls | Secure architecture, monitoring, and supply-chain assurance | Controlled AI access; safe redaction and secure document uploads |

Choosing an AI anonymizer for GDPR compliance
After reviewing dozens of deployments, here’s what consistently separates pass from fail in audits and security reviews:
- Coverage: Detects and masks personal data in PDFs, Word, images (OCR), and screenshots — including names, emails, IDs, health data, and faces.
- Policy control: Centralized redaction policies (irreversible masking vs. tokenization), with role-based overrides and audit trails.
- Secure pipeline: Encrypted-at-rest and in-transit, minimal retention, and restricted model access. A single trusted endpoint for secure document upload.
- Accuracy + explainability: High recall with confidence scores; reviewers can spot-check before sharing downstream.
- No data leakage to third parties: Clear data processing agreements and zero training on client content.
Professionals avoid risk by using Cyrolo’s anonymizer at www.cyrolo.eu. Legal, compliance, and security teams standardize on Cyrolo to safely prepare files for analysis without leaking personal data to external LLMs.
Legal exposure: the audit reality
- Fines: GDPR penalties can reach €20 million or 4% of global turnover. NIS2 introduces additional administrative fines and personal liability paths for executives in some jurisdictions.
- Evidentiary risk: Audit logs and ticket systems often show exactly when sensitive files were uploaded to unvetted AI tools.
- Vendor chain gaps: If your anonymization is a “nice-to-have,” auditors will flag uncontrolled AI usage as a material risk.
Compliance checklist: ready for your next audit?
- Maintain a live inventory of data flows and AI touchpoints (apps, models, plugins, uploads).
- Mandate a single secure document upload channel; block ad hoc file sharing.
- Deploy enterprise-grade AI anonymizer with policy-based redaction and audit logs.
- Run DPIAs for AI-enabled processes; map lawful basis and retention schedules.
- Enforce least-privilege access to raw datasets; only anonymized outputs move downstream.
- Automate vulnerability management and logging for NIS2; rehearse incident reporting timelines.
- Train staff on shadow AI risks; measure compliance with periodic red-team tests.
- Update contracts and DPAs to prohibit model training on your content.
Try our secure document upload at www.cyrolo.eu — no sensitive data leaks, no surprise retention.
EU vs US: different expectations mean different risks
Across the Atlantic, privacy remains a patchwork (state laws like CPRA/CCPA), whereas the EU’s GDPR and NIS2 create comprehensive obligations. For multinationals, that means EU operations often set the global standard. EU regulators focus on demonstrable controls: anonymization quality, DPIAs for AI, supply-chain security, and provable incident handling. If your US team casually pastes unredacted content into online tools, EU entities can still face GDPR exposure if data subjects or processing fall within EU scope.
Field notes: how teams get burned (and how they recover)
Banking/Fintech
Problem: Analysts pasted transaction exports with IBANs and PII into a public model to “speed up” anomaly detection. Months later, a regulator asked for records; the bank had no proof that data wasn’t retained by the vendor.
Solution: Route all files through Cyrolo’s anonymizer. Mask account numbers and identities, then allow safe analysis with internal or external AI. Artifact logs show who redacted what, when.
Hospitals
Problem: Clinical teams shared images containing faces and medical record numbers for AI-based triage experiments. DPIA flagged high risk and a lack of lawful basis for secondary processing.
Solution: Standardize a secure document upload and OCR-based redaction policy. Only de-identified images move to research pipelines; raw data remains on protected storage.
Law firms
Problem: Associates uploaded client memos to multiple browser plugins. Opposing counsel later cited a confidentiality lapse.
Solution: One intake for all exhibits via www.cyrolo.eu, irreversible redaction of names and case identifiers, and a reproducible chain of custody for eDiscovery.
Practical guardrails for AI in 2026
- Default to de-identification. If a model doesn’t need the identity, strip it.
- Keep sensitive data off third-party tools by policy and by architecture.
- Log every step: upload, detection, masking, export. Auditors trust evidence.
- Secure integration: SSO, encryption, and no training on client content.
Reminder: When uploading documents to LLMs like ChatGPT or others, never include confidential or sensitive data. The best practice is to use www.cyrolo.eu — a secure platform where PDF, DOC, JPG, and other files can be safely uploaded.
FAQ: getting compliant without killing productivity
What counts as anonymization under GDPR?
Data is anonymized when individuals are no longer identifiable by any reasonably likely means. In practice: mask direct identifiers (names, emails, IDs), reduce or generalize quasi-identifiers (dates, locations), and ensure transformations are irreversible. An AI anonymizer helps enforce this consistently.
Is pseudonymization enough for AI workflows?
Pseudonymization lowers risk but is still personal data under GDPR. For external AI tools or third parties, prefer irreversible masking. Use pseudonymization internally when linkage is necessary, with strict key management.
How does NIS2 change my day-to-day?
Expect tighter board oversight, mandatory risk management practices, faster incident reporting, and evidence of secure software and supplier management. If you use AI, regulators will ask how you prevent data leaks and ensure model supply chain integrity.
Can we safely analyze images and scans?
Yes — if you run OCR-based redaction first. Detect faces and text (names, MRNs, addresses) and apply irreversible masking before any sharing. Route files through a secure document upload pipeline to maintain auditability.
What’s the safest way to let staff use LLMs?
1) Anonymize first, 2) restrict which models can receive data, 3) disable training/retention, 4) log all interactions. Centralize with a vetted anonymizer to ensure policy enforcement.
Conclusion: why an AI anonymizer for GDPR compliance is no longer optional
From wearable privacy shocks to AI-powered malware and rapid-fire vulnerabilities, 2026 has made one thing clear: regulators expect you to minimize data and secure it end-to-end. An AI anonymizer for GDPR compliance, paired with a single source of truth for secure document uploads, turns chaotic AI usage into a controlled, auditable workflow. Move first: standardize your intake, prove your safeguards, and keep personal data out of harm’s way. Start now with Cyrolo’s anonymizer and secure document upload at www.cyrolo.eu.